Hypervisor Crack Denuvo – How It Works & What You Need Download
You want to play Denuvo-protected titles without modifying executables. The hypervisor crack does that. It operates at Ring -1, below your OS, intercepting CPU instructions and feeding fake results to Denuvo. It's not a traditional patch. It's something else entirely.
This Hypervisor Crack Denuvo guide breaks the method down. What it is, how it differs from proper cracks, what your PC needs, and the exact setup process.
Hypervisor Crack Denuvo Download - Guide
This guide covers version 2025-2026 hypervisor bypasses for titles like Black Myth: Wukong, Stellar Blade, Borderlands 4, and Crimson Desert. No file size listed - the guide itself is text. No DLC included. The guide explains everything you need.
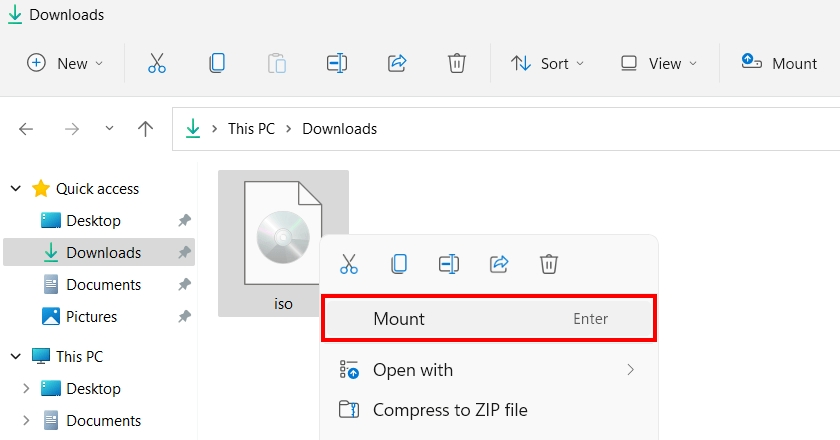
- Download the guide archive
- Extract using 7-Zip or WinRAR
- Enable hardware virtualization in BIOS
- Run VBS.cmd setup script
- Reboot and launch the game via provided launcher
System Requirements
- CPU: Must support VT-x (Intel) or AMD-V/SVM (AMD)
- OS: Windows 10 or 11
- BIOS: Hardware virtualization enabled
- Secure Boot: Can stay enabled
How Hypervisor Cracks Work
The crack loads a custom unsigned kernel driver. It places a lightweight hypervisor on your CPU at Ring -1. From there it intercepts CPUID queries, RDTSC timing, MSR reads, and KUSER_SHARED_DATA. Each gets a spoofed response. On AMD systems, SimpleSvm.sys handles it. On Intel, hyperkd.sys with hyperhv.dll does the job. KIRIGIRI.dll injects a fake license token into Denuvo's verification routine.
Every license check returns valid. The game thinks everything is fine. Denuvo is still there - it just gets lied to from underneath. Honestly? That's clever. When you close the game, the hypervisor devirtualizes all cores and unloads. Clean exit. The disabled Windows security features stay off until you run the revert option. Yeah, that happens.
A proper Denuvo crack patches the executable directly. One file. No drivers, no system changes. Hypervisor cracks leave game files untouched but require setup. You trade convenience for compatibility with uncracked titles.
Windows VBS must be disabled. Memory Integrity, Credential Guard, Windows Hello, and Driver Signature Enforcement all need to go. The VBS.cmd script handles this. It also adds a boot entry to prevent the Windows hypervisor from loading. Trust me on this - run the revert when you are done playing.
Available in English.
This guide is for anyone tired of waiting for proper cracks. If you can enable virtualization in BIOS and run a script, you can play titles that have resisted traditional patching for months. Not for the faint of heart, but worth it if you know what you are doing. The Hypervisor Crack Denuvo method works right now.